Cloud 3.0: beyond “lift‑and‑shift” to sovereignty
The cloud has entered Cloud 3.0 — a phase where it is no longer just about moving to the cloud, but about controlling where data lives, how it is governed, and who can access it.
In this era, multi‑cloud sovereignty is rising to the top of the CEO agenda, reshaping board‑level discussions on risk, compliance, and resilience.
Cloud 1.0 was about cost savings and scalability.
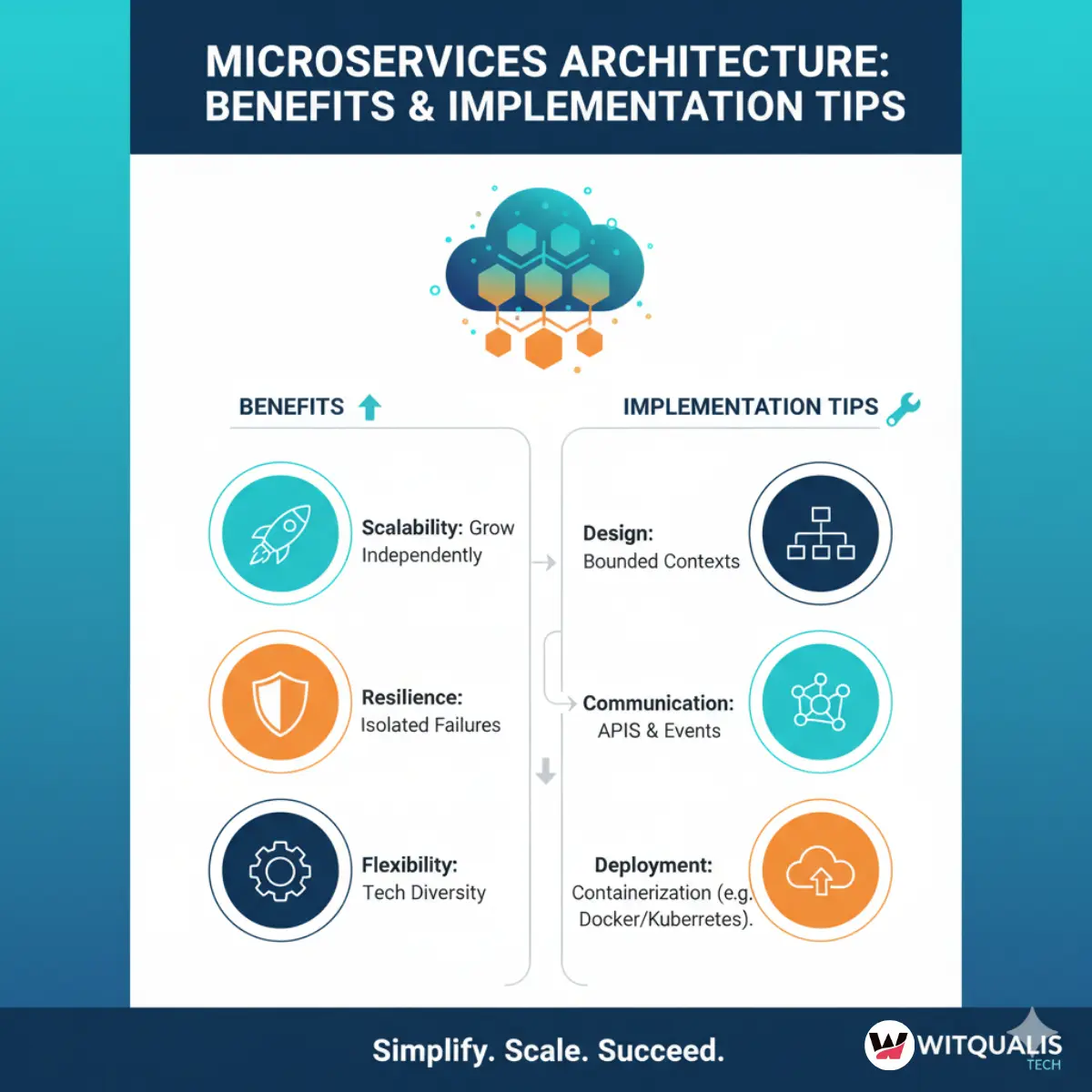
>Cloud 2.0 was about agility, DevOps, and containerization.
>Cloud 3.0 is about sovereignty, control, and governance across multiple clouds.
For CEOs, this means:
-
Cloud strategy is no longer an IT topic; it is a board‑room and legal‑compliance topic.
-
Choosing one large hyperscaler is no longer enough; multi‑cloud and hybrid strategies are the default.
-
Data sovereignty, residency, and access‑control rules are now as important as uptime and performance.
At the same time, this transformation is putting enormous pressure on internal teams.
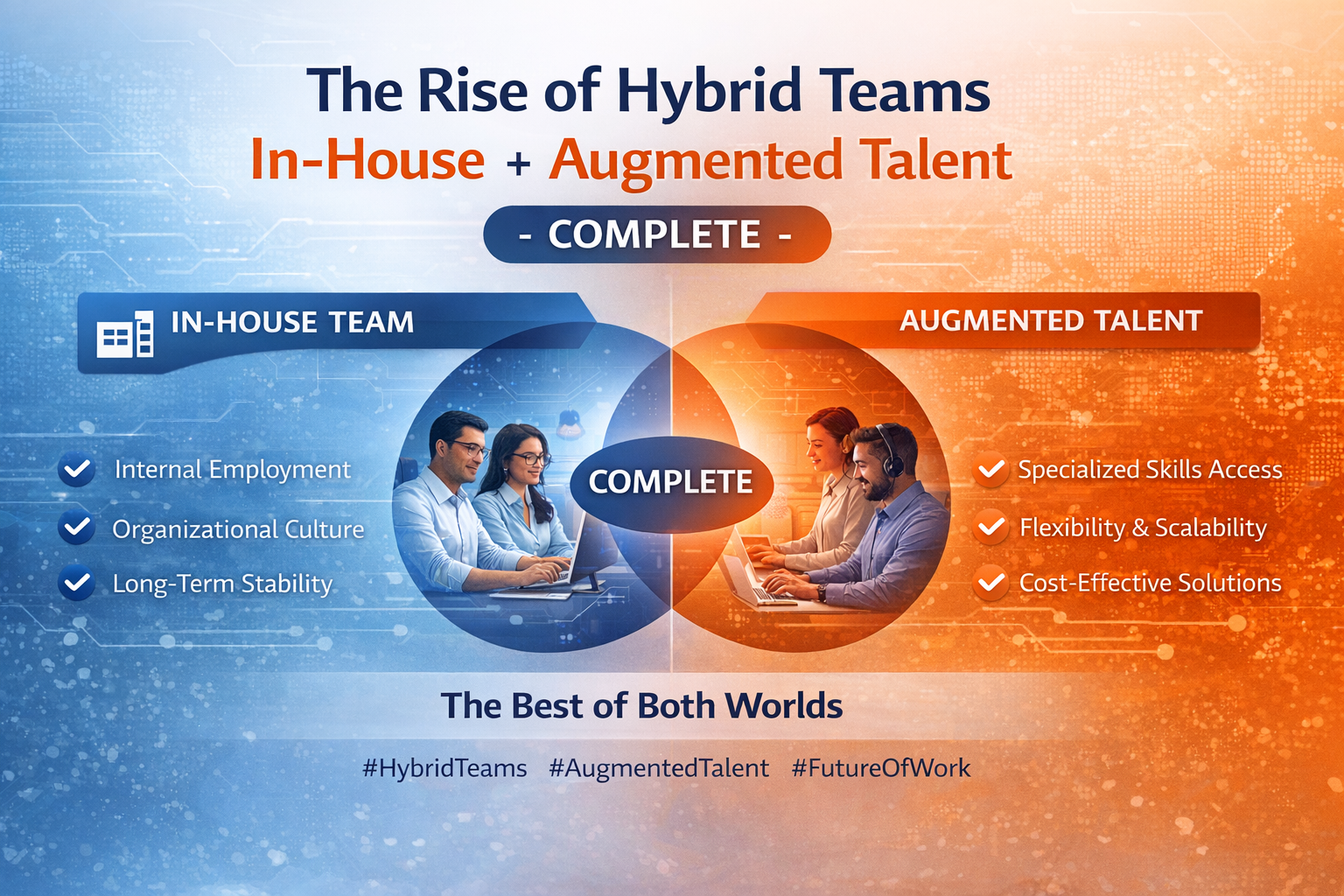
Most organisations do not have enough cloud‑architecture, security‑policy, and compliance‑governance talent in‑house to design and manage multi‑cloud‑sovereign landscapes.
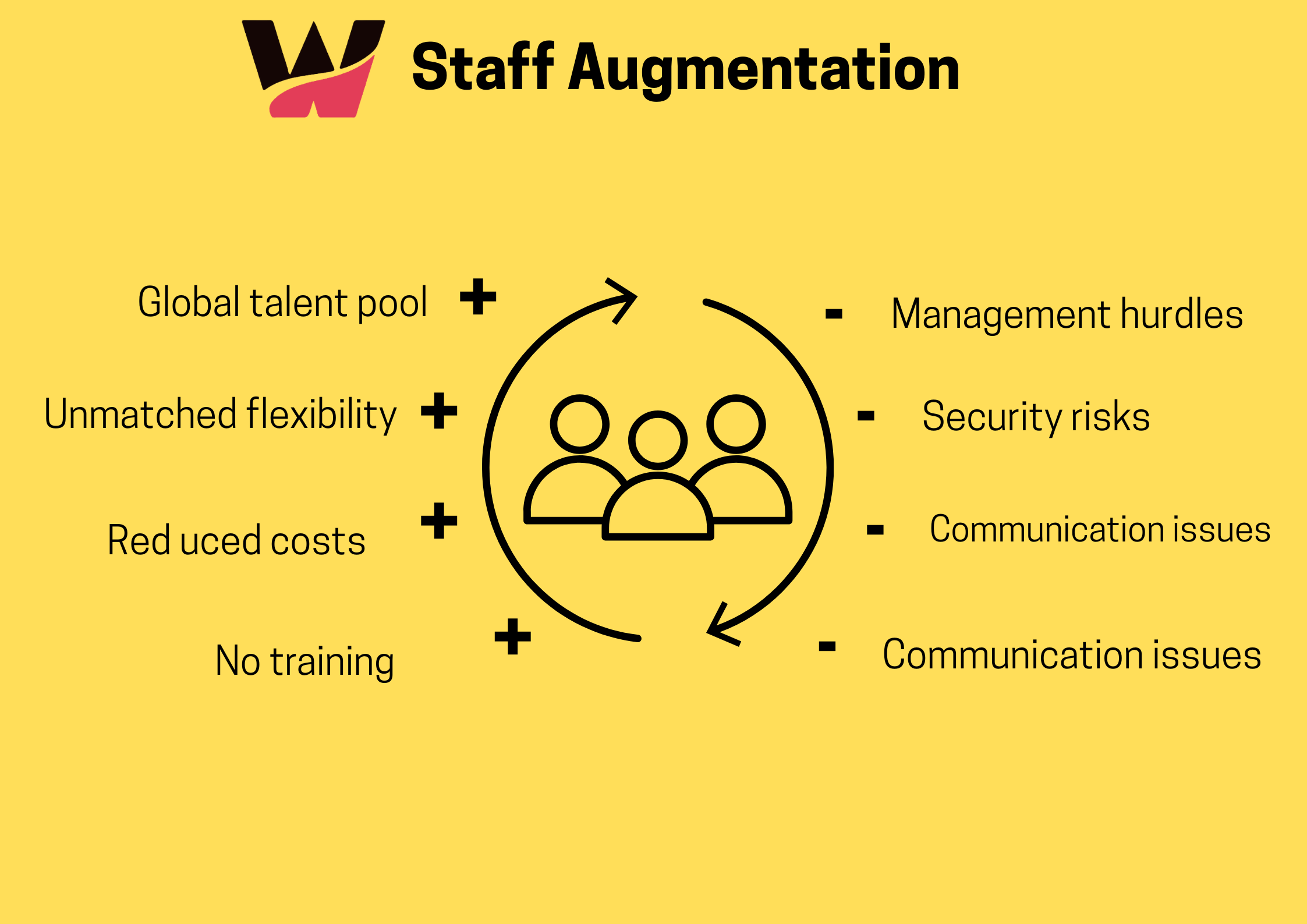
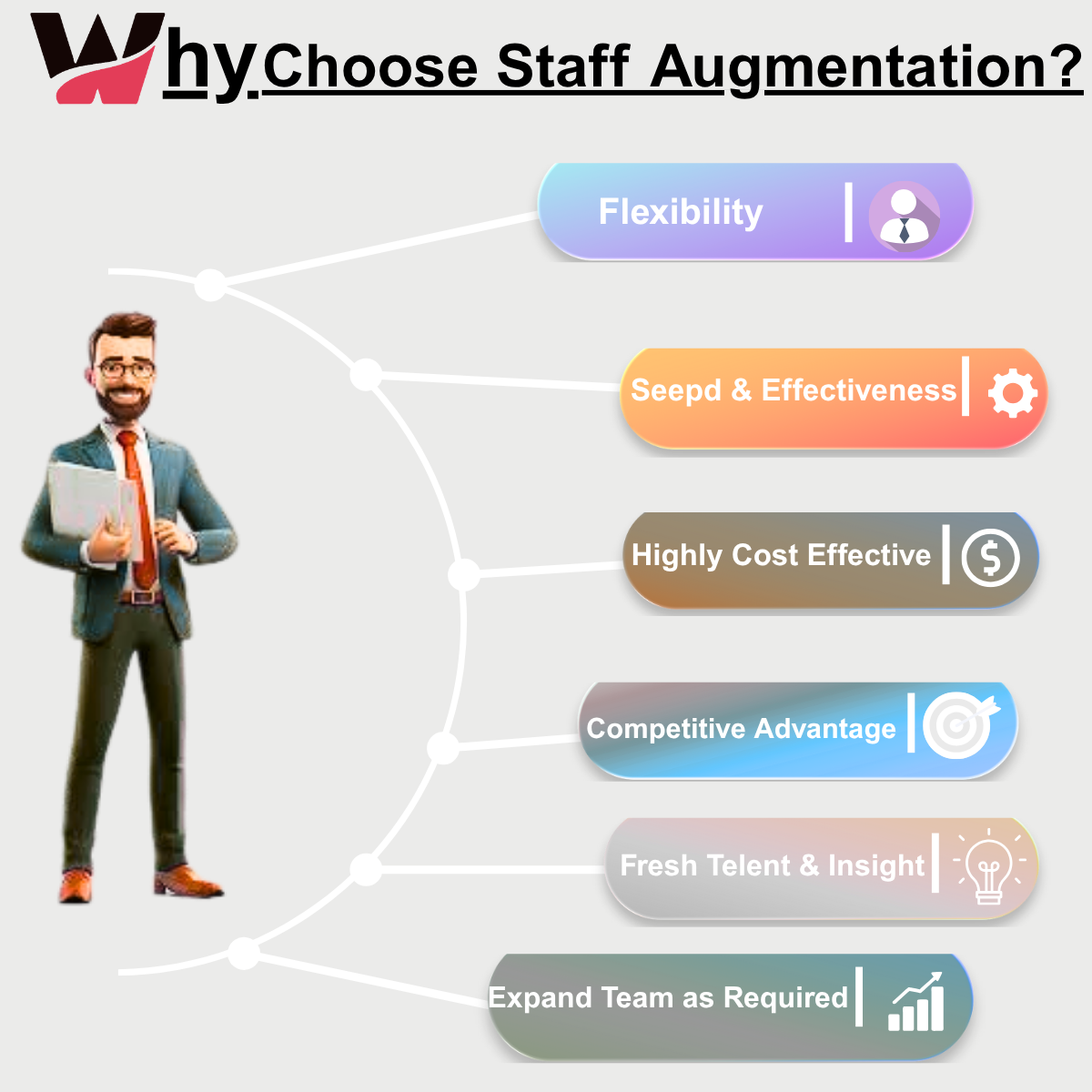
That’s where IT staff augmentation and staff augmentation services come in.
Through IT staff augmentation companies, CEOs and CIOs can access cloud‑sovereignty‑ready specialists without the long‑term HR overhead of building everything in‑house.
What is multi‑cloud sovereignty (and why it matters to CEOs)
Multi‑cloud sovereignty defined
Multi‑cloud sovereignty is the ability to:
-
Run workloads across multiple cloud providers and on‑premises environments,
-
Maintain strict control over data location, jurisdiction, and access,
-
And enforce compliance with local and global regulations (e.g., GDPR, DPDP, CCPA, sector‑specific rules).
Unlike “multi‑cloud” strategies that simply focus on avoiding vendor lock‑in, multi‑cloud sovereignty is concerned with:
-
Who owns the data,
-
Where it is stored and processed,
-
And who can legally access it.
For a CEO, this is not just a technical detail — it is a reputational, regulatory, and financial risk issue.
A data‑residency violation or a cross‑border‑data‑flow incident can trigger fines, customer‑trust erosion, and even business‑model changes.
Why sovereignty is now a CEO‑level priority
Several trends have elevated sovereignty to the CEO level:
-
Stricter data‑privacy and data‑localization laws in Europe, India, the US, and other regions.
-
Geopolitical risks, including sanctions, export controls, and jurisdictional conflicts over cloud infrastructure.
-
Industry‑specific regulations in finance, healthcare, and critical infrastructure, where data cannot leave certain borders.
-
Customer expectations that personal data will be handled lawfully and transparently.
In this environment, CEOs can no longer treat cloud as a “utility” that IT can manage independently.
Cloud‑strategy decisions now directly affect:
-
Legal and compliance posture,
-
M&A and expansion plans,
-
And even national‑level licensing and permitting.
The rise of Cloud 3.0: multi‑cloud, hybrid, and sovereign
The evolution from Cloud 1.0 to Cloud 3.0
-
Cloud 1.0 (≈2010–2016)
Focused on cost reduction and resource‑elasticity.
The question was: “Can we move workloads to the cloud to save money?” -
Cloud 2.0 (≈2017–2022)
Focused on agility, DevOps, containers, and microservices.
The question was: “How fast can we ship new features in the cloud?” -
Cloud 3.0 (≈2023–now)
Focused on sovereignty, governance, and resilience.
The question is: “Where can we run this workload, under which laws, and under whose control?”
Cloud 3.0 does not negate the earlier benefits; it adds a new layer of governance on top of existing cloud and hybrid architectures.
What multi‑cloud sovereignty looks like in practice
A typical multi‑cloud‑sovereign environment might look like:
-
Workloads are split across clouds and on‑premises:
-
Core transactional systems in a local‑cloud region that meets data‑residency rules.
-
AI / analytics workloads in a global hyperscaler region where advanced GPU and data‑services are available.
-
Legacy applications on‑premises, behind controlled egress and encryption.
-
-
Data is tagged and governed by policy:
-
Personal data is stored only in pre‑approved regions.
-
Anonymized or synthetic data can be used in global environments.
-
Access controls follow least‑privilege and just‑in‑time principles.
-
-
Governance is automated and auditable:
-
Policy‑as‑code defines where data can be stored and processed.
-
Real‑time observability shows where workloads and data actually are.
-
Audit trails are available for legal and compliance teams.
-
For a CEO, this is not just “cloud architecture” — it is a business‑governance system that must be monitored and managed at the highest level.
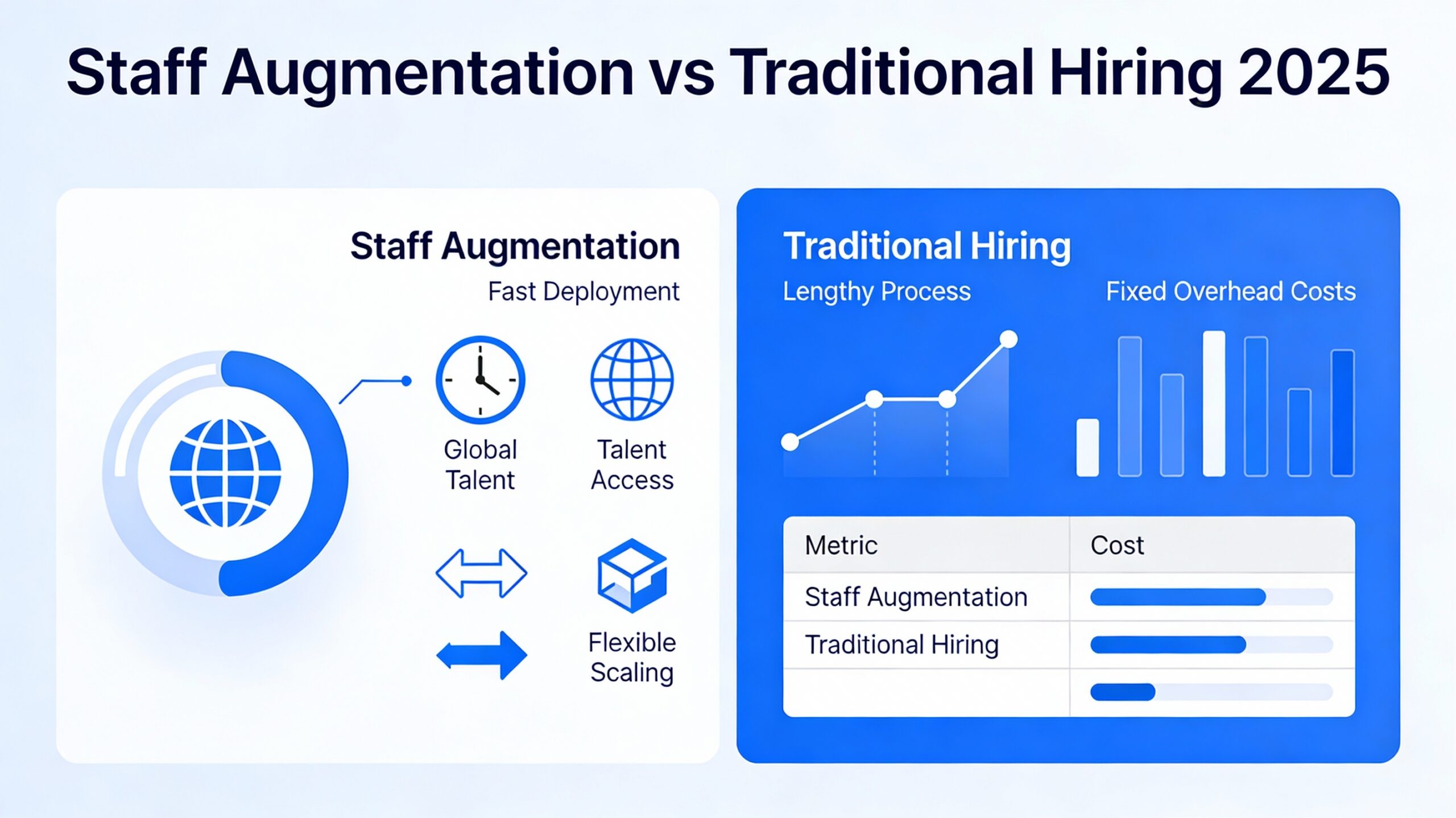
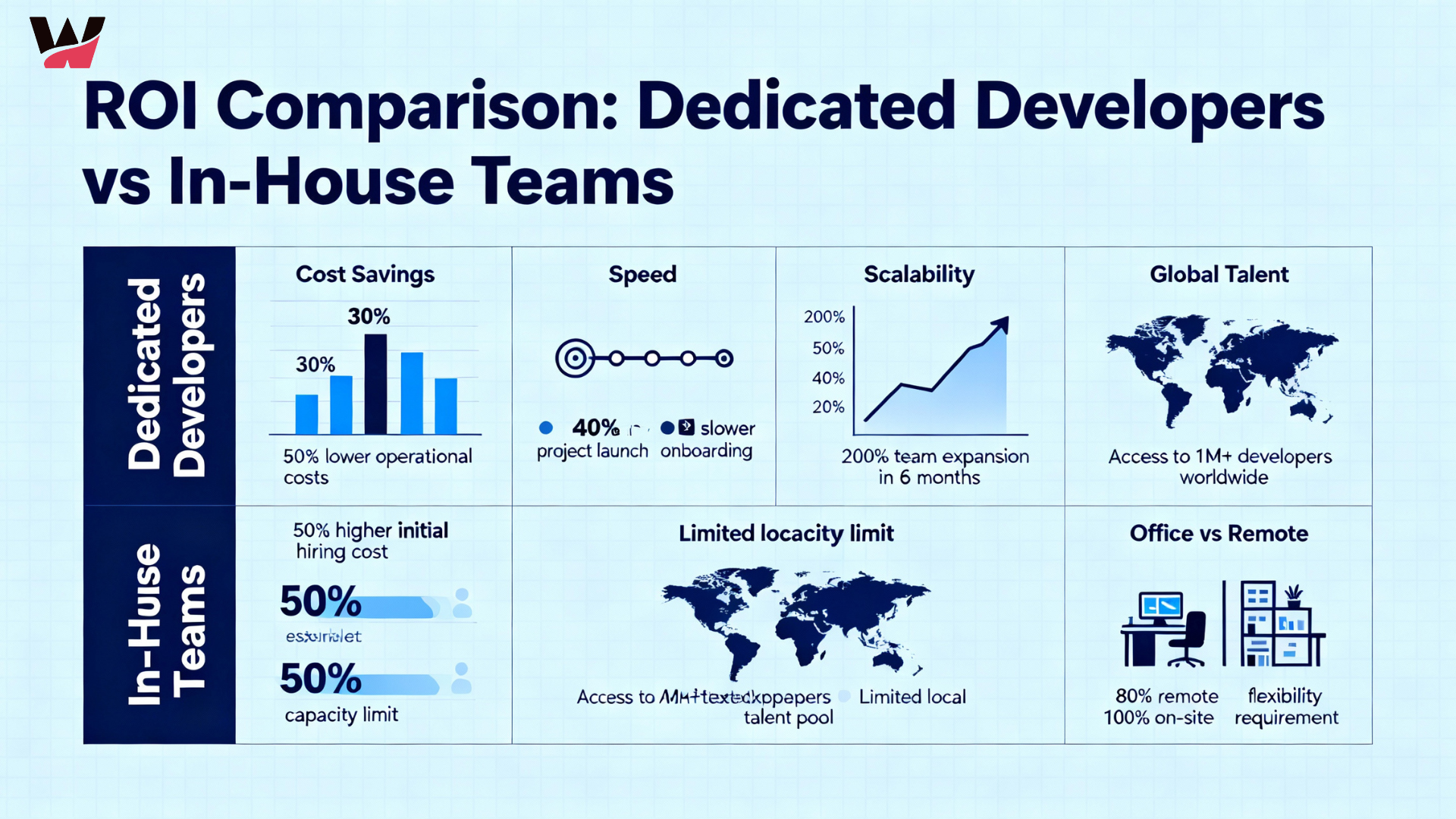
Why multi‑cloud sovereignty is hard to build in‑house
Talent shortages in cloud‑sovereignty roles
Building a multi‑cloud‑sovereign environment requires:
-
Cloud‑architecture and multi‑cloud design experts.
-
Security and compliance‑policy specialists.
-
Data‑governance and data‑sovereignty engineers.
-
DevSecOps and policy‑as‑code practitioners.
-
Legal and regulatory‑advisory support (often in‑house counsel or external partners).
These skills are:
-
Rare,
-
Expensive,
-
and hard to retain over long periods.
Most organisations cannot hire enough of these specialists permanently to design, implement, and maintain multi‑cloud‑sovereign architectures at the scale required.
Fast‑moving regulatory and cloud landscapes
Cloud‑provider roadmaps and regulatory frameworks are evolving constantly.
New regions are launched, new services are introduced, and new data‑privacy rules are enacted.
Internal teams often struggle to:
-
Keep up with cloud‑provider updates,
-
Interpret regulatory changes,
-
And translate them into technical architecture and governance rules.
A “one‑and‑done” migration project is no longer sufficient.
Cloud‑sovereignty initiatives must be continuous, iterative, and adaptive.
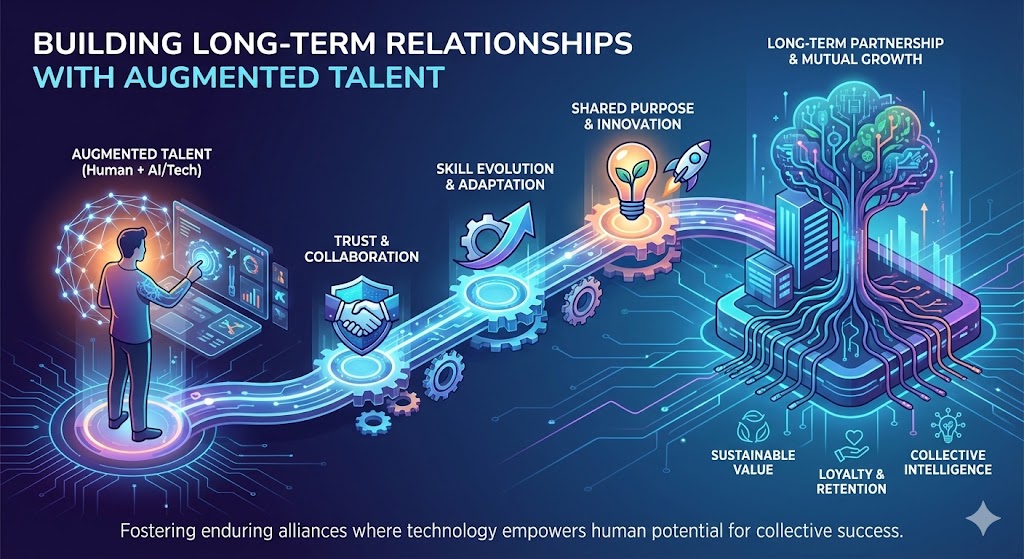
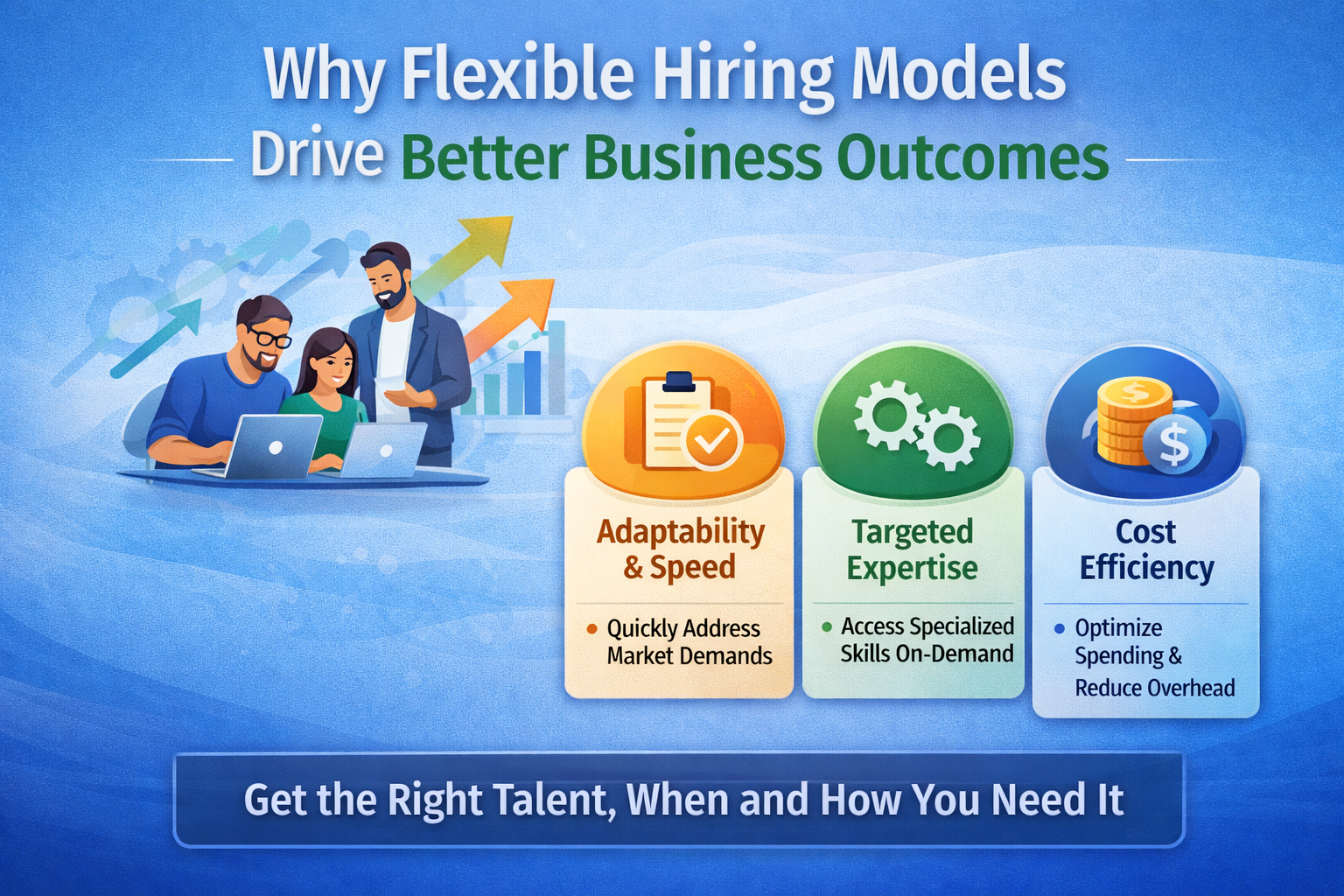
How IT staff augmentation supports Cloud 3.0 and multi‑cloud sovereignty
Staff augmentation services for cloud‑sovereign teams
IT staff augmentation is a natural fit for Cloud 3.0 projects because:
-
It is project‑ and strategy‑driven, not just “body‑count.”
-
It allows organisations to scale up specialized talent for critical phases (design, migration, compliance‑tightening).
-
It can be scaled down once the platform is stable and governance is automated.
Through staff augmentation services, CEOs and CIOs can access:
-
Cloud‑architecture specialists who design multi‑cloud‑sovereign patterns.
-
Security and compliance‑policy engineers who define and enforce data‑residency and access rules.
-
DevSecOps and automation engineers who implement policy‑as‑code, observability, and audit‑trails.
-
Cloud‑migration engineers who move workloads while respecting sovereignty constraints.
These specialists are embedded into existing cloud and cybersecurity teams, working under the client’s governance and tools.
IT staff augmentation companies as multi‑cloud‑sovereign partners
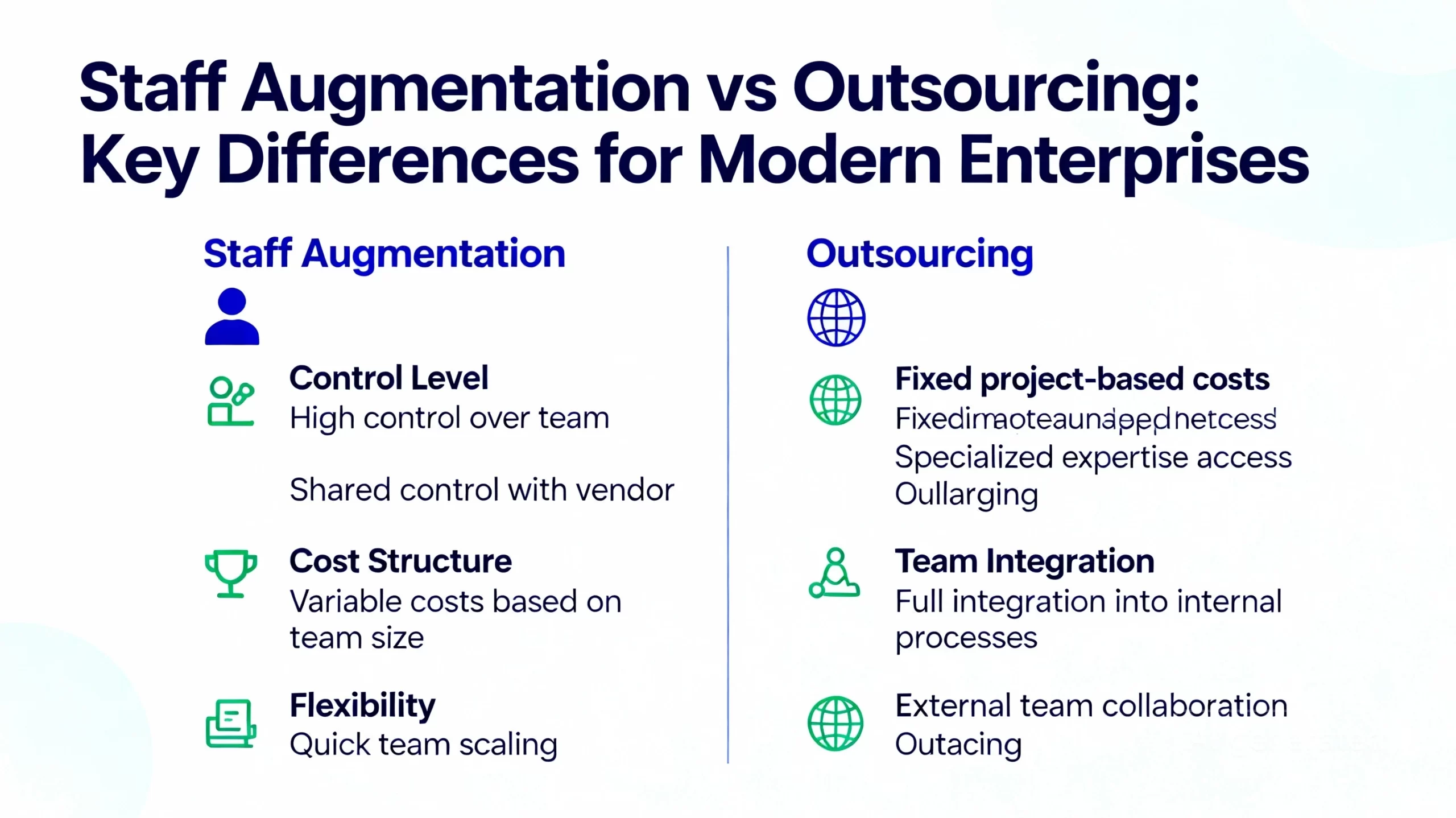
Unlike generic staff augmentation companies such as Orange Mantra and Yoma Business Solutions — which often focus on mainstream software‑development and support roles — IT staff augmentation companies that specialise in Cloud 3.0 and sovereignty bring:
-
Deep understanding of data‑residency, GDPR‑style regulations, and local‑law constraints.
-
Experience designing multi‑cloud and hybrid architectures that are explicitly built for sovereignty.
-
Track records of working with large enterprises, financial institutions, and regulated industries.
For a CEO, this is a key differentiator:
Cloud‑sovereignty is not a “nice‑to‑have” feature; it is a core business‑risk issue.
Partnering with a staff augmentation provider that understands this at a strategic level is far more valuable than working with a generic “staff‑augmentation‑as‑a‑recruiter‑plus” vendor.
Wirqualis focuses precisely on this intersection: Cloud 3.0, multi‑cloud sovereignty, and IT staff augmentation. [https://www.wirqualis.com]
Wirqualis and Cloud 3.0: an IT staff augmentation perspective
Wirqualis positions itself as a partner for Cloud 3.0‑ready organisations that need to move to multi‑cloud‑sovereign environments without over‑hiring. [https://www.wirqualis.com]
Through its IT staff augmentation services, Wirqualis helps clients:
-
Design multi‑cloud and hybrid architectures that respect data‑sovereignty and regulatory requirements.
-
Implement policy‑as‑code, observability, and audit‑trail mechanisms across cloud environments.
-
Migrate workloads in phases, with clear governance over where data lives and how it is accessed.
Wirqualis’ staff augmentation process is tailored for:
-
Short‑ to medium‑term engagements that align with multi‑cloud‑sovereignty milestones.
-
Deep integration with client teams, tools, and governance models.
-
Knowledge transfer and handover so that internal teams can maintain and evolve the environment.
Compared with more traditional staff augmentation companies, Wirqualis emphasises:
-
Strategic alignment with CEO‑level priorities (risk, compliance, sovereignty).
-
Technical depth in cloud‑architecture, security‑policy, and data‑governance.
-
Structured engagements that map clearly to business‑governance outcomes.
For CEOs and CIOs, this means:
-
They can temporarily scale up multi‑cloud‑sovereign expertise without bloating permanent headcount.
-
Internal teams remain in control of strategy and governance.
-
Long‑term risk is reduced because the environment is built with sovereignty by design.
The staff augmentation process for Cloud 3.0 projects
– Needs assessment and governance‑risk mapping
-
Business and legal teams define:
-
Where data can and cannot be stored.
-
Which workloads are subject to which regulations.
-
What resilience and continuity requirements exist.
-
-
Cloud and security teams assess:
-
Current cloud‑provider mix.
-
Existing data‑flows and residency patterns.
-
This phase ensures that multi‑cloud sovereignty is treated as a risk‑governance question, not just a technical decision.
– Role definition and sourcing via IT staff augmentation
-
Required skills are mapped:
-
Cloud‑architecture and multi‑cloud design.
-
Data‑governance and policy‑as‑code.
-
Security‑compliance and observability.
-
-
IT staff augmentation companies are engaged to:
-
Source and vet specialists with the right domain and regulatory experience.
-
Ensure they can work under the client’s governance and tools.
-
– Embedded delivery and multi‑cloud design
-
Augmented staff are embedded into cloud and security squads.
-
They design:
-
Zone‑based architecture (sovereign regions, non‑sovereign regions, on‑premises).
-
Data‑classification and tagging schemas.
-
Policy‑as‑code definitions for where data can be stored and processed.
-
– Migration, compliance‑tightening, and audit readiness
-
Workloads are migrated in phases, with clear rules for data‑egress and encryption.
-
Automation and observability tools are configured to show:
-
Where data actually lives.
-
Who is accessing which systems.
-
-
Audit‑trail and reporting capabilities are built for legal and compliance teams.
– Knowledge transfer and long‑term governance
-
Once the platform is stable, augmented staff may be scaled back.
-
Internal teams are trained in:
-
Maintaining multi‑cloud‑sovereign patterns.
-
Updating policies as regulations evolve.
-
This end‑to‑end staff augmentation process ensures that Cloud 3.0 journeys are strategic, compliant, and manageable without long‑term HR bloat.
Practical next steps for CEOs and CIOs
-
Map your data‑sovereignty and regulatory requirements by geography and industry.
-
Audit your current cloud‑footprint and identify where data‑residency rules are being challenged.
-
Engage IT staff augmentation companies that have experience in multi‑cloud‑sovereign architecture and governance, not just generic cloud‑migration roles. Witqualis
-
Run a pilot multi‑cloud‑sovereign pattern for one critical workload or region.
-
Scale the model across the business as governance and audit‑readiness improve.
LinkedIn‑optimized version (with hashtags)
Below is a shorter, LinkedIn‑ready version of this content, optimised for engagement and readability.
Moving to Cloud 3.0: Why Multi‑Cloud Sovereignty Is the CEO’s New Priority
Cloud is no longer just about cost and agility.
In Cloud 3.0, the CEO’s real concern is sovereignty:
-
Where data lives,
-
Under which laws,
-
And who can access it.
Multi‑cloud sovereignty — the ability to run workloads across multiple clouds and on‑premises while respecting data‑residency and compliance rules — is now a board‑room priority.
For many organisations, building this capability in‑house is too slow and too expensive.
Cloud‑sovereignty‑ready talent is rare, and regulatory landscapes are evolving fast.
That’s where IT staff augmentation and staff augmentation services come in.
Through IT staff augmentation companies, CEOs and CIOs can:
-
Access cloud‑architecture, security‑policy, and data‑governance specialists without over‑hiring.
-
Build multi‑cloud‑sovereign architectures that are compliant, auditable, and resilient.
Wirqualis supports organisations in their Cloud 3.0 journeys, helping them design and implement multi‑cloud‑sovereign environments with the right mix of internal and augmented talent. witqualis
Is cloud‑sovereignty already on your CEO’s agenda — or is it still treated as an IT‑only topic?






























































[…] Cloud-native threat detection. […]
[…] Cloud strategy and multi‑cloud consulting […]